This article is written by Arshdeep Bedi ( Student of the final year -Punjabi University, Patiala)
INTRODUCTION
The internet, computers, mobiles, and other forms of technology have revolutionized every aspect of human life from decades including how we communicate, shop, obtain news, entertain our self etc. This technological advancement has also created innumerable opportunities for offenders to commit various forms of crime. Online crimes are often referred to as cybercrime. The main cause of cybercrimes is our dependency on it, of which the perpetrator takes advantage and uses his special knowledge of cyberspace for committing the crime. The first case of cybercrime has appeared in Yahoo!, Inc. vs Akash Arora & Anr, 1999
What is a Cybercrime
Cybercrime can be defined as any type of illegal activity that takes place via digital means. Cybercrime is a Criminal activity that either targets individuals, or organizations, or society. Some of the examples of cybercrime are cyberstalking, cyber terrorism against a government organization, online gambling, committing fraud, trafficking in child pornography, intellectual property, stealing identities or violating the privacy, etc.
Types of Cybercrime
- HACKING: It is unauthorized access or control over a computer or someone’s network security systems for some illegal purpose.
- PHISHING: It is a practice where a person having fraudulent intent of sending emails creating fake web pages to be from a known company or a a well-known company in order to induce an individual to get some personal information or some passwords such as credit cards, etc.
- IDENTITY THEFT: The fraudulent exercise of using personal information in order to obtain credit, loans etc.
LAWS RELATED TO CYBERCRIME
Our Indian laws have not defined the term cybercrime but an act has been introduced to tackle types of cyber crimes and such act is INFORMATION TECHNOLOGY ACT 2000 and IPC can also be used to prosecute against cybercrimes or to supplement provisions to the IT act.
For instance: offences like hacking, data theft and virus attack could be prosecuted under sec 6 read with sec 43 of the IT act. Some of the provisions stated in the act are:
- Sec 65: Tampering with computers source and code documents: This section applies to people who intentionally conceals, alters or destroy any computer source and code using any network or program.
Punishment for such crime is imprisonment for 3 years or 2 lakh fine or both.
- Sec 67: Penalizes publication and transmission of obscene material or material containing sexually explicit acts and of material depicting children in sexually explicit acts in electronic form.
Punishment can be up to 7 years or fine that can be up to 10 lakh.
- Sec 72: Breach of confidentiality and privacy: A person with secured access to any electronic record, information, or any other material discloses it with other people without their consent.
Punishment imprisonment up to 2 years or fine up to 1 lakh.
ARE INDIAN LAWS ARE STRICT ENOUGH TO CURB THE CYBER CRIMES?
NO, Indian laws are not strict enough to curb cybercrimes. There are provisions related to various cyber crimes but there are few loopholes in those provisions which are not strict enough to deal with cybercrime. For instance: sec 66E of IPC wherein it as mentioned that capturing should be nonconsensual and as opposed to that, it has been seen in most of the cases where images are taken with consent in the past, of which convicted person will take advantage of it and publishes on the internet, this is also called revenge porn.
In the modern era, people are using technology for revenge if these types of laws exist then it’s difficult to stop cybercrimes and cybercrime has expanded its roots to almost every aspect of the life of netizens. Even in Shreya Singhal V Union of India, 2015 it was contended that any matter posted on the internet is universally accessible than any other media to the netizens, it is not confined to any particular boundary, unlike any other media. It, therefore, becomes obvious that this requires more and strict regulations because there is a growth of scammers, phishing, money laundering, etc. If we compare Indian cyber laws with any other country then our laws are not strict enough to deal with the crimes. For instance: in Indian punishment for child pornography under the protection of children from sexual offences (POSCO) act 2012 is imprisonment up to 5 years for a first conviction whereas in USA imprisonment up to 15 to 30 years for the first conviction.
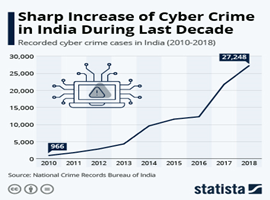
As per the data, the conviction in cases cybercrime in India continues to less. If systems continue in the same manner means it will become difficult to tackle the growing crime rate. Apart from all the legal aspect, the important thing to be done is awareness on the individual level. According to the reports, most of the government officials are not aware of their adjudicating powers under IT act. Unless each person doesn’t become aware and cautious it will be difficult to regulate the crimes.
Issues yet to be covered under the Information and Technology Act
Information and Technology Act and Amendment Act are the landmark first step and milestone in the technological growth of the nation. But at the same time, the existing law is not sufficient. It would not be a new thing to say that our laws are not so efficiently to provide proper protection. Even in the act, there are many issues which are still to be touched or are completely untouched.
Territorial Jurisdiction
TerritorialJurisdiction is the major issue which has not been properly addressed by the legislation. Jurisdiction of the officer as per Sections 46, 48, 57 and 61 in the relation to adjudication process and the appellate procedure under Section 80 is not sufficient as though they provide the police officers with the powers to enter, search a public place for a cybercrime etc. But since cyber crimes which are computer-based crimes and if the mail of one is hacked in one place by accused in another state, determination of concerned Police station is needed that who will take cognizance. One can’t ignore the fact that the investigators generally try to avoid acceptance of such complaints on the grounds of jurisdiction itself. Since the crime is borderless and territory free and generally in matter of few seconds gets changed into territories of several jurisdictions which is commonly seen. There is a need for proper training is to be given to all the police officers and the authority in relation to it. Moreover, the jurisdiction should not be a bar in arresting the convict.
Some of the strict laws and amendments which help to prevent the crime:
- The matter on social media is confined and can be accessed from anywhere, so lawmakers should impose restrictions on accessibility or limit it so that abuses can be reduced.
- Judicial proceedings on such matters have to be specific.
- More advance training to be given to police officials on this subject.
- The term of imprisonment should be increased for some crimes.
- If possible a special court shall be introduced to deal with these cases separately and also there will be no unwanted accumulation of cases, which we already have.
- Improvise the standard procedure for seizing and analysis the digital evidence.
How to protect oneself against cybercrimes
The best ways to protect your computer and your personal data are:
- Software and system updated
software and operating system must be up to date so as to ensure benefit from the latest security.
- Use of anti-virus software
Using anti-virus is a smart way to protect your system from attacks. If one uses anti-virus software, it must be updated so to get the best level of protection.
- Use of strong passwords
strong passwords must be used that can’t be guessed and must not be recorded anywhere.
- Never open attachments in spam emails
The computers generally is infected by malware attacks and another cybercrime is via email attachments that are present in spam emails. The attachment from a sender who is unknown must not be opened.
- Links in spam emails stop clicking them!
Another way by which people become victim of cybercrime is by clicking on links in spam emails or other messages. To be safe these must be avoided.
- Do not give personal information unless it is secure
personal data must not or never be given over the phone or via email unless one is completely sure the line or email is secure.
- Contact companies directly about suspicious requests
Generally, it is seen that many times call comes from fake numbers who claim to be the real company personals. Their calls must not be picked or the necessary info must not be given.
- Be mindful of website URLs
URLs you are clicking on must be clicked without proper knowledge proper care is needed to check them. Do they look legitimate? Avoid clicking on links with unfamiliar or spams looking URLs.
Conclusion
Society and its citizens are today happening to be more and more dependent upon technology. More use of technology beings the crime based on electronic offences. Even though one tried to avoid them but they keep on peeping in. The undertaking of law-making machinery of the nation which we all know is not sufficient even to curb all the crimes, which is still in the developing stage. The care towards the crimes of the cyber world is also needed to be addressed as efficiently as the others. The laws should be proper and effective. Hence, there should be the persistent efforts of rulers and lawmakers to ensure that laws of technology must contain aspect and issues in relation to cybercrimes. A constant vigil and eye must be kept on the issue. The issue seems to be very minute but actually, it is not. The issue gives rise to many other crimes also. So proper address to such crime is essential and need of the hour.
Latest Posts
- Job opportunity at EXO Edge, Sahibzada Ajit Singh Nagar, Punjab, India: Apply Now!!
- Internship opportunity at Vishwas Advisors, Kalyan, Maharashtra, India: Apply Now!!
- Internship opportunity at Kulfi Collective, Mumbai, Maharashtra, India: Apply Now!
- Job opportunity at The Neotia University, Diamond Harbour, West Bengal, India: Apply Now !!
- Job opportunity at Morgan Stanley, Mumbai, Maharashtra, India: Apply Now!!
- Job opportunity at VISA INTELLIGENCE CONSULTANCY LLP, New Delhi, Delhi, India: Apply Now!!
- Job opportunity at Amazon Web Services (AWS), Gurugram, Haryana, India: Apply Now!!
- Job opportunity at Stelcore Management Services Private Limited, Mumbai, Maharashtra, India: Apply Now!!
- Job opportunity at Zscaler, Sahibzada Ajit Singh Nagar, Punjab, India: Apply Now!!
- Job opportunity at Irish Expert, Delhi, India: Apply Now!!
- Job opportunity at UnitedLex · Gurgaon, Haryana, India: Apply Now!
- Internship opportunity at Vineforce · Nabha, Punjab, India: Apply Now!!
- ACEDY (1)
- CLAT-Peeps! (10)
- Current Affairs (2)
- competitions (132)
- Conferences and Seminars (201)
- Webinar (1)
- Course and Workshops (107)
- Debates (46)
- DEGY (1)
- Eassy Competitions (69)
- Fellowships & Scholarships (56)
- Guest Blogs (6)
- important (29)
- Internships and Jobs (2,317)
- interviews (8)
- LEGY (1)
- moot court (180)
- Opportuintes (2,731)
- Job Opportunity (1,191)
- opportunity (2,559)
- Call for papers (475)
- Quizes,fests and others (298)
- Work Opportunity (836)
- Our Blog (1,049)
- Administrative Law (17)
- ADR (13)
- Arms Act (2)
- Case Analysis (205)
- Company law (36)
- Constitutional Law (143)
- Consumer Protection Act (17)
- Contract Law (62)
- CPC (10)
- Criminal Law (140)
- Cyber Law (13)
- Environmental Laws (30)
- Evidence Act (20)
- Family Law (12)
- General (205)
- International Humanitarian Law (8)
- International law (23)
- IPR (10)
- Jurisprudence (13)
- labor laws (7)
- Maritime Laws (1)
- Partnership Act (2)
- personal law (33)
- Taxation (10)
- Tort (64)
- Transfer of Property (2)
- Our Services (11)
- career advice (2)
- others (6)
- Top Stories (524)
- Uncategorized (720)
Archives
- November 2023
- October 2023
- September 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- March 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- February 2020
- January 2020
- November 2019